8 steps to protect businesses against WannaCry and other cyberattacks
This piece is presented by SDN Communications.
The international WannaCry cyberattack made headlines for its size and quick spread but it hasn’t proven to be the most successful. Still, there are lessons to learn from the event that likely left some businesses scrambling to determine whether they were vulnerable and others dealing with the aftermath of being victimized.
The basics
U.S. Homeland Security officials say at this point, the attack has affected more than 300,000 machines in 150 countries, including the United States, United Kingdom, Spain, Russia, Taiwan, France and Japan.
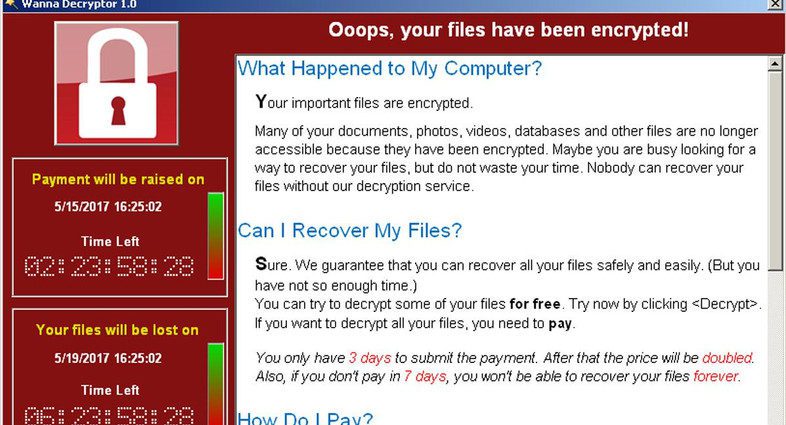
Like many forms of ransomware, WannaCry encrypts the target data so the user can’t access it and demands a ransom payment in exchange for the decryption key. According to various open sources, the requested ransom for this variant is .1781 bitcoins or about $300 U.S. dollars. Websites monitoring the accounts show funds are coming and crossed over $80,000 on Wednesday.
How does WannaCry spread?
It’s unclear whether all of the ways WannaCry spreads have been exposed. Initial reports indicated the first infection was the result of a traditional phishing email. However, security researchers have not found an example of such an email. Instead, it’s also suggested the initial and secondary infections across the Local Area Network may be from internet scanning for open ports and susceptible systems. Regardless of the source, WannaCry works its way around the local network using a known vulnerability in Microsoft operating systems dubbed “Eternal Blue.” Microsoft released a patch in March. More recent reports indicated variants also may use the “DoublePulsar” backdoor outlined in the April ShadowBrokers data leak.
What can I do to protect myself and business?
Cybercriminals are counting on human error to help spread malware. The best thing you can do is educate and practice a layered approach to defense:
- Learn to identify and report suspicious emails and train staff to avoid clicking on suspicious links or attachments.
- Make sure all devices on your network are properly patched with up-to-date software.
- Install (MS17-010) from Microsoft, which closes the vulnerability suspected to be at play in this attack.
- Use endpoint security that include anti-virus and anti-malware and update your signatures regularly.
- Use a next generation firewall with regularly updated signatures and be sure to scan incoming and outgoing traffic for infected attachments.
- Consider blocking legacy protocols on local networks and incoming SMB traffic on port 445. Additionally, filtering NetBIOS port 139 and RDP 3389 may help.
- Consider segmenting your network and following least privilege practices.
- Backup regularly and validate your backups to ensure they operate as expected.
SDN Communications helps its customers rest easier when cyberthreats like this pop up. Customers with certain levels of Managed Firewall services may already enjoy the anti-virus, malware and intrusion protection recommended above. On Friday during the peak of the attack, SDN’s experts proactively updated the anti-virus and IPS signatures released earlier in the day as preventative measure.
SDN also has staff members who monitor cyberthreats and attacks at all hours, everyday. They continue to monitor and analyze this evolving threat and others, and will share that knowledge at an upcoming event.
Attend SDN’s free UPTIME University session in Sioux Falls on the morning of Tuesday, May 23, to review the WannaCry attack, discover resources to protect your organization and get a first look at how other cyberthreats are targeting businesses in the region. Register now for free.
UPTIME University: Harness the Power of the Network
Tuesday, May 23, 2017 | Doors open at 7:30 a.m.
Hilton Garden Inn Downtown